Audit Trail Is Not a Chain of Custody
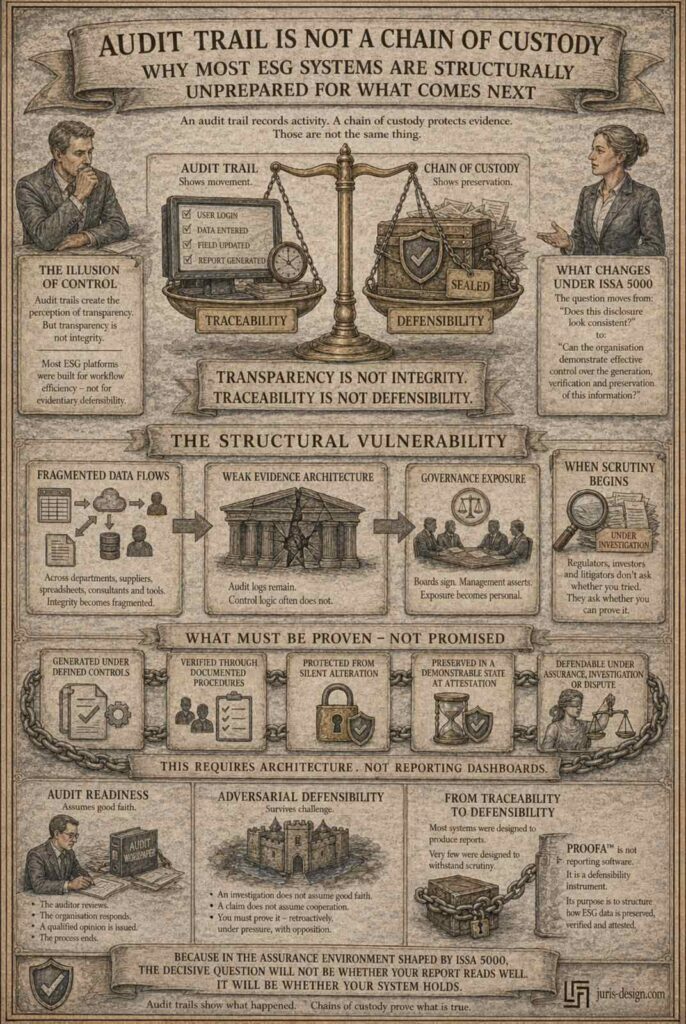
Why Most ESG Systems Are Structurally Unprepared for What Comes Next
Most companies believe they are ESG-ready because their system has an audit trail.
That belief is dangerously incomplete.
An audit trail records activity.
A chain of custody protects evidence.
Those are not the same thing.
And as ESG reporting moves toward higher levels of assurance under ISSA 5000, this distinction stops being technical - and becomes legal.
The Illusion of Control
An audit trail typically shows:
- who entered data
- who edited it
- when changes were made
This creates a perception of transparency.
But transparency is not integrity.
A forensic chain of custody answers different questions:
- Was the original data preserved?
- Could it be altered without detection?
- Was access restricted and documented?
- Can the organisation demonstrate the state of the data at the moment management signed the report?
Most ESG platforms were built for workflow efficiency and disclosure consolidation.
They were not built for evidentiary defensibility.
That difference rarely matters - until scrutiny begins.
What Changes Under ISSA 5000
ISSA 5000 shifts the focus from narrative coherence to control demonstration.
The question moves from:
“Does this disclosure look consistent?”
to:
“Can the organisation demonstrate effective control over the generation, verification and preservation of this information?”
As sustainability reporting frameworks - including those introduced under the Corporate Sustainability Reporting Directive - move toward progressively stronger assurance expectations, systems will not be evaluated only on outputs.
They will be evaluated on architecture.
When ESG data flows across departments, suppliers, spreadsheets, external consultants and digital tools, integrity becomes fragmented.
Audit logs remain.
Control logic often does not.
When Governance Meets Evidence
Board members sign sustainability reports.
Management asserts that controls are in place.
But here is the structural question rarely asked at board level:
Can we demonstrate that our ESG data is legally defensible - not merely traceable?
Traceability shows movement.
Defensibility shows preservation.
If a sustainability claim is challenged - by regulators, investors or in litigation - the issue will not be whether the data was entered in good faith.
The issue will be whether the organisation can prove that the information was:
- generated under defined controls
- verified through documented procedures
- protected from silent alteration
- preserved in a demonstrable state at the time of attestation
That requires architecture.
Not reporting dashboards.
The Hidden Exposure
As sustainability disclosures integrate into governance and director oversight duties under instruments such as Directive 2013/34/EU, ESG systems become part of corporate accountability infrastructure.
This is no longer an IT question.
It is not a communications question.
It is a governance question.
Because once management signs, assertions move from operational to personal.
And personal exposure is rarely mitigated by an audit trail alone.
The Structural Vulnerability
We are entering a phase where:
- ESG disclosures are assured, not merely published.
- Sustainability claims are litigated, not merely criticised.
- AI tools assist in generating data and narratives - while responsibility remains human.
In this environment, weak evidence architecture is not a technical inconvenience.
It is a structural vulnerability.
Most organisations do not recognise the gap - because their systems have never been tested under adversarial conditions.
Yet.
The Audit Assumption
External assurance assumes good faith and cooperation.
The auditor reviews. The organisation responds. A qualified opinion is issued. The process ends.
But the scenarios that create real organisational exposure do not operate on those terms.
A regulatory investigation does not assume good faith.
An investor claim does not assume cooperation.
A greenwashing proceeding does not ask whether the report looked consistent when it was filed.
It asks whether the organisation can prove - retroactively, under pressure, with an opposing party actively looking for failures - that every data point was generated under defined controls, protected from alteration, and preserved in a demonstrable state.
Audit readiness and adversarial defensibility are not the same thing.
Most organisations have designed for the first.
Almost none have designed for the second.
From Traceability to Defensibility
Most ESG systems were designed to produce reports.
Very few were designed to withstand scrutiny.
PROOFA™ was developed as a legal-operational instrument integrating forensic standards, ESG disclosure logic under the Corporate Sustainability Reporting Directive, and Evidence Architecture™ methodology into one structured framework.
It is not reporting software.
It is a defensibility instrument.
Its purpose is not to generate sustainability claims - but to structure how ESG data is preserved, verified and attested in a manner capable of withstanding assurance, investigation or dispute.
Because in the assurance environment shaped by ISSA 5000, the decisive question will not be whether your report reads well.
It will be whether your system holds.
Does your organisation have an audit trail - or a true forensic chain of custody for ESG data?
Other blogs
Audit Trail Is Not a Chain of Custody
Most companies believe they are ESG ready because their system has an audit trail...
US Supreme Court vs. Executive Branch: What Balkan Exporters Need to Know
Analysis of the decision Learning Resources, Inc. v. Trump and its operational consequences...
